Talk about Mithril security solutions for this industry
Discover more
Protection of an E-commerce site from DDoS attacks
A fast-growing retail e-commerce website suffers a DDoS attack: the adoption of the Mithril WAF solution help the client to respond and immediately block the attack.
INDUSTRY: E-Commerce – Retail
E-commerce sites are the most likely victims of cyber-attacks: growing rapidly and with many orders to handle every day, especially after the pandemic due to Covid-19. This type of business that are very sensitive to operation interruptions: even a few minutes of inactivity might generate very significant economic damage. It may even happen in some cases that a competitor could have an interest in blocking the operation of another e-commerce, organizing a DDoS attack with services that can now be easily purchased thanks to resources available on the dark web.
Distributed Denial of Service (DDoS) attacks are a particular type of DoS (literally, distributed denial of service). These attacks have the aim of making a web service unusable, which in the case of an e-commerce results in the impossibility of managing purchases orders for the entire duration of the attack, and often even after it. In fact, to conduct this attack, attackers overload the victim’s computer system by generating unusual traffic, preventing legitimate users from accessing it. The peculiarity of a DDoS attack is that the source is difficult to locate, as the attack is launched from multiple origins at the same time.
DDoS attack protection: the solutions of competitors vs Mithril
The Customer is victim of DoS attacks on their main e-commerce, most likely orchestrated by competitors. Almost every day at 00:00 and 15:30 they receive a volumetric attack so large that the servers hosting the site saturate and stop responding for hours, causing loss of orders and customers.
HOW OTHER SOLUTIONS WORK
The client already had a WAF service running offered by a well-known Mithril competitor, but was unable to stop the attack. The WAF service in use by the customer in fact activated as countermeasure the banning of some countries and the Javascript challenge to block the “bad bots”. However, this countermeasure did not solve the problem neither allow the customer to face the attack. Moreover, customer’s server got saturated and also created the “empty carts” issue. The WAF JavaScript challenge, in fact, generated a courtesy page that informed users that they were checking their browser and asked them to wait a few seconds. As a consequence, users began to leave the website without waiting, causing economic damage to the customer.
DDoS ATTACKS: HOW MITHRIL WORKS
After that, the Customer decides to adopt the Mithril WAF solution: as soon as it was configured, it began to intercept the first two attacks. The methods and times were the same: the first attack at 3.30 pm and the second at about midnight. Mithril managed to automatically scale and manage traffic correctly all the time, without giving the slightest disservice to the customer, who in the meantime was normally processing the online orders.
Each attack was of incredible proportions: hundreds of thousands of compromised servers generating about 6 million requests each and hundreds of thousands of simultaneous connections.
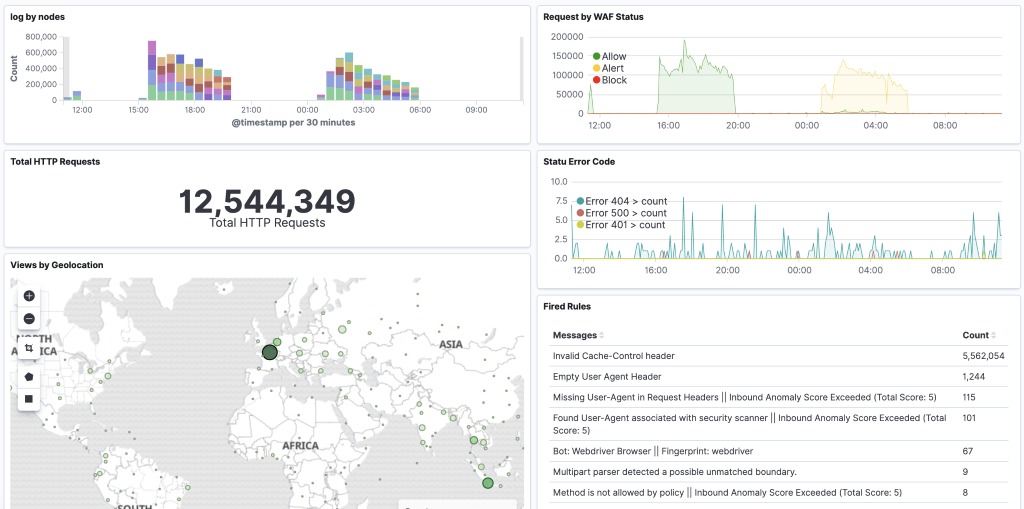
In the graph “Request by Waf” at the top right of the image, in yellow you can see that the second attack was identified by a custom rule written by the Mithril team, taking advantage of a request generation error committed by the creators of the botnet. Pretending to be a “real browser”, they have compiled a request header provided, however, only in the response from the RFC of the HTTP protocol. In this way, the Mithril team was able to identify the entire botnet with a single rule.
WHY MITHRIL IS A RELIABLE WAF SOLUTION AGAINST DDoS ATTACKS
The solution proposed by Mithril has delivered the following countermeasures:
⦁ enhanced the Mithril challenge javascript: it no longer shows the courtesy page (like other competitors solutions), but instead downloads the client’s homepage every hour and uses it as an HTML page for the challenge. In addition to this, it identifies the human user based on the interaction (mouse, scroll, keyboard, graphic card, etc …)
⦁ implemented an autoscaling system of the WAF nodes that allowed to balance the normal load on 2 nodes and to scale up to 12 nodes as the occupation of resources increases.
⦁ enhanced the log collection part, to allow more accurate and targeted analyzes based on customer needs.
These solutions allowed the customer to identify and block the attack, restoring the full operation of the business in a very short time.
The graph of simultaneous connections received by the cloud hosting service is impressive: there were spikes of 80K and 70K simultaneous connections to the Client’s site as can be seen from this graph which shows the normal operation of the site and the spikes generated by the attack.
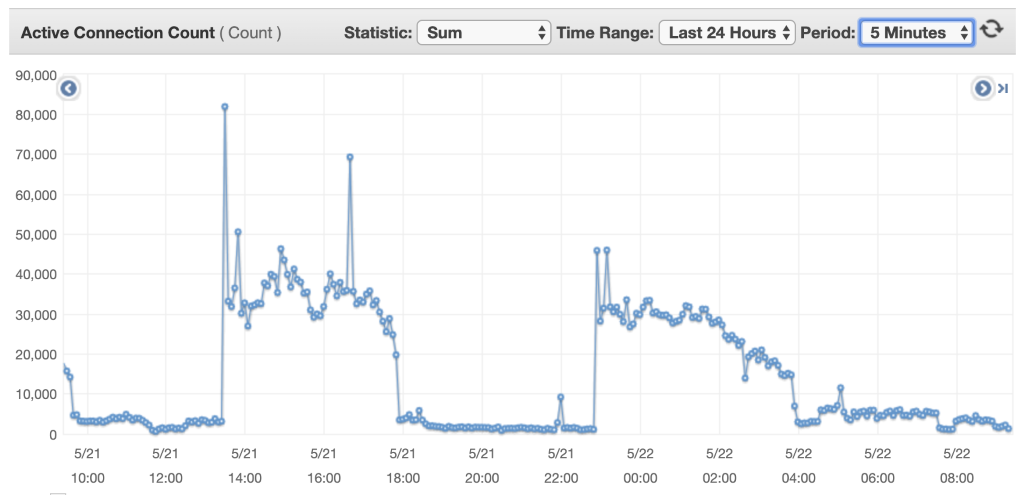
During both attacks (12 million requests that never reached the client’s servers), Mithril allowed the site to continue running without interruption, leaving the client’ servers with very low traffic during the attacks, thanks to Mithril active protection.